Transforming Spaces, One Breath at a Time
Our real-time air quality monitors, EC fans, and electronic filtration systems work together to deliver the purest air possible
Our real-time air quality monitors, EC fans, and electronic filtration systems work together to deliver the purest air possible


Our real-time air quality monitors, EC fans, and electronic filtration systems work together to deliver the purest air possible
Our WELL-compliant monitors deliver highly accurate sensor readings, feature Wi-Fi connectivity, and boast a sleek glass finish that complements any interior
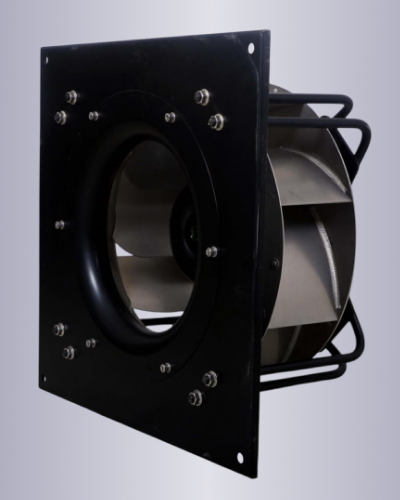
Our best in class high efficiency, high performance EC fans are ideal for purified air ventilation

Our WELL Compliant sensors are best in class and provide the needed accuracy to get any project certified

Market Leading efficiency with minimal heat emissions and perform well even at partial loads

Our monitors allow for demand control ventilation making the overall system very energy efficient while maximizing occupant comfort

Our Wi-fi enabled AQI monitors are tightly integrated with our EC fans, providing unparalleled hardware software integration, resulting in best in class performance.
This article provides a deep dive into what XWorm is, what the 56main variant signifies, how the ZIP distribution works, and—most importantly—exactly what happens during the installation process. Before analyzing the installation string, we must understand the malware. XWorm is a sophisticated Remote Access Trojan (RAT) written in the .NET framework (C#). It first appeared in 2020 and has since evolved into one of the most popular malware-as-a-service (MaaS) offerings on the dark web.
This article is provided for educational and defensive cybersecurity purposes only. The author and publisher do not endorse, support, or encourage any illegal activities, including unauthorized access to computer systems. Installing malware on a system you do not own is a criminal offense. The Complete Breakdown: Understanding the "xworm56mainzip install" Phenomenon In the dark corners of cybercrime forums, specific strings of text become infamous. One such string that has recently garnered attention among security analysts is "xworm56mainzip install" . At first glance, it looks like a random concatenation of a malware family name, a version number, and an archive format. However, for threat actors and blue teams alike, this string represents a specific attack vector.
For the average user, the rule is simple: Never open a ZIP file from an untrusted source. For security professionals, the rule is equally simple: Hunt for the conf.bin and the memory-scraping behavior of XWorm.
"Ready to improve your indoor air quality? Get in touch with us today to explore our certified IAQ solutions. Breathe easier, live healthier—contact us now!"
This article provides a deep dive into what XWorm is, what the 56main variant signifies, how the ZIP distribution works, and—most importantly—exactly what happens during the installation process. Before analyzing the installation string, we must understand the malware. XWorm is a sophisticated Remote Access Trojan (RAT) written in the .NET framework (C#). It first appeared in 2020 and has since evolved into one of the most popular malware-as-a-service (MaaS) offerings on the dark web.
This article is provided for educational and defensive cybersecurity purposes only. The author and publisher do not endorse, support, or encourage any illegal activities, including unauthorized access to computer systems. Installing malware on a system you do not own is a criminal offense. The Complete Breakdown: Understanding the "xworm56mainzip install" Phenomenon In the dark corners of cybercrime forums, specific strings of text become infamous. One such string that has recently garnered attention among security analysts is "xworm56mainzip install" . At first glance, it looks like a random concatenation of a malware family name, a version number, and an archive format. However, for threat actors and blue teams alike, this string represents a specific attack vector.
For the average user, the rule is simple: Never open a ZIP file from an untrusted source. For security professionals, the rule is equally simple: Hunt for the conf.bin and the memory-scraping behavior of XWorm.