Show Focus Points
2019 update released! Check out download page for details
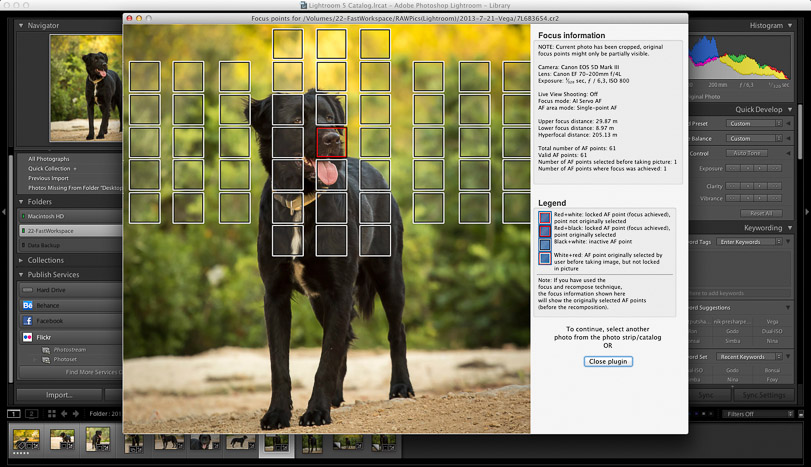
Show Focus Points is a plugin for Adobe Lightroom. It shows you which focus points were selected by your camera when the photo was taken.
Show Focus Points
2019 update released! Check out download page for details
Show Focus Points is a plugin for Adobe Lightroom. It shows you which focus points were selected by your camera when the photo was taken.
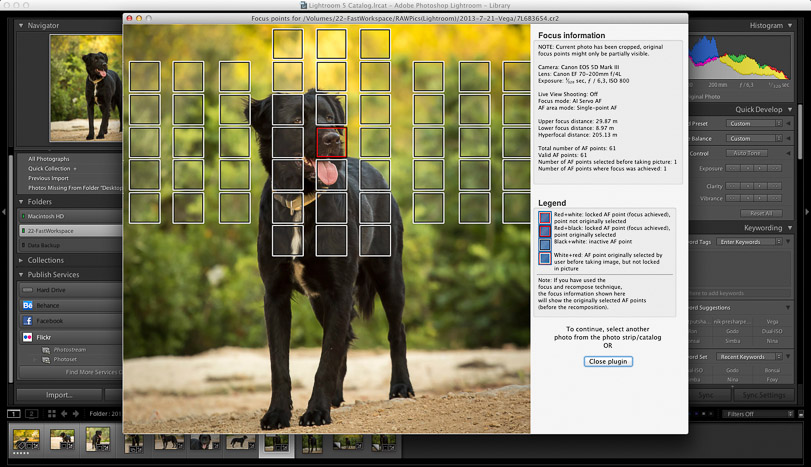
Show Focus Points is a plugin for Adobe Lightroom which shows you which of your camera's focus points were used when you took a picture.
Below find some screenshots of the plugin in action.
Click on the images to enlarge them.
Download Mac-only version (6.6 MB)
Download Windows-only version (14 MB)
Download version containing both Mac+Windows versions (20 MB)
For deeper analysis:
To provide you with a genuinely helpful, long-form article, I will pivot to the most probable intended interpretations of your keyword, explain how real verification works for MP4 files, and offer a deep dive into MP4 integrity checks, codec authentication, and security best practices. i adn564mp4 verified
I understand you’re looking for a long article centered around the keyword However, after a thorough review of current technical databases, software version histories, codec libraries (like FFmpeg, H.264, H.265), and platform verification systems (such as those used by YouTube, Facebook, Twitter, or Instagram), there is no known standard technology, file format, or verification protocol associated with the string "adn564mp4." For deeper analysis: To provide you with a
Remember: In digital media, verification is a , not a product. No single string can replace proper validation. Have questions about MP4 verification or need help analyzing a suspicious file? Leave a comment below or consult a digital forensics professional. Have questions about MP4 verification or need help
It appears this phrase may be a typo, a unique internal identifier, a placeholder, or a string from an unofficial or malicious source (e.g., fake “file verifier” tools, scam CAPTCHAs, or cracked software forums).
mp4box -info file.mp4 This shows all boxes, track IDs, and codec details. If the tool cannot parse ftyp or moov , the file is invalid. To prove a video came from a trusted source (e.g., a news agency or bodycam), you need a digital signature (like PGP or JWT) attached to the file or its hash. The string “verified” alone is meaningless without a cryptographic chain of trust. Part 3: The Danger of Unverified “Verification” Strings Scammers often exploit the concept of “verification” to trick users. 3.1 Fake CAPTCHA and Verification Scams A common attack: a website or pop-up displays: “Your file i_adn564mp4 is not verified. Press Win + R and run the command below to verify.” The command is often malicious (e.g., downloading and executing a script). Legitimate MP4 verification never requires you to run system commands from a random website. 3.2 Malicious MP4 Files Hackers can embed exploits in MP4 files (e.g., heap spray attacks via malformed stts boxes). A “verified” label on a pirated or untrusted site is no guarantee of safety.
For deeper analysis:
To provide you with a genuinely helpful, long-form article, I will pivot to the most probable intended interpretations of your keyword, explain how real verification works for MP4 files, and offer a deep dive into MP4 integrity checks, codec authentication, and security best practices.
I understand you’re looking for a long article centered around the keyword However, after a thorough review of current technical databases, software version histories, codec libraries (like FFmpeg, H.264, H.265), and platform verification systems (such as those used by YouTube, Facebook, Twitter, or Instagram), there is no known standard technology, file format, or verification protocol associated with the string "adn564mp4."
Remember: In digital media, verification is a , not a product. No single string can replace proper validation. Have questions about MP4 verification or need help analyzing a suspicious file? Leave a comment below or consult a digital forensics professional.
It appears this phrase may be a typo, a unique internal identifier, a placeholder, or a string from an unofficial or malicious source (e.g., fake “file verifier” tools, scam CAPTCHAs, or cracked software forums).
mp4box -info file.mp4 This shows all boxes, track IDs, and codec details. If the tool cannot parse ftyp or moov , the file is invalid. To prove a video came from a trusted source (e.g., a news agency or bodycam), you need a digital signature (like PGP or JWT) attached to the file or its hash. The string “verified” alone is meaningless without a cryptographic chain of trust. Part 3: The Danger of Unverified “Verification” Strings Scammers often exploit the concept of “verification” to trick users. 3.1 Fake CAPTCHA and Verification Scams A common attack: a website or pop-up displays: “Your file i_adn564mp4 is not verified. Press Win + R and run the command below to verify.” The command is often malicious (e.g., downloading and executing a script). Legitimate MP4 verification never requires you to run system commands from a random website. 3.2 Malicious MP4 Files Hackers can embed exploits in MP4 files (e.g., heap spray attacks via malformed stts boxes). A “verified” label on a pirated or untrusted site is no guarantee of safety.